Tor is a free application and open network that helps to protect your anonymity online.
If you access an internet resource without using Tor then you'll give away your IP address. This may reveal something about your location and can be used to spot you when you return to that resource. In addition, anyone watching your internet connection will be able to record the sites that you visit.
With Tor installed, though, it's a very different story. Internet traffic that leaves your PC will go first to the Tor network, so anyone spying on your connection won't see the sites you're accessing. That traffic will then bounce randomly around various Tor relays, which means your request cannot be tracked. And when it reaches the destination your data request will contain an IP address that leads back to the Tor network: not you.
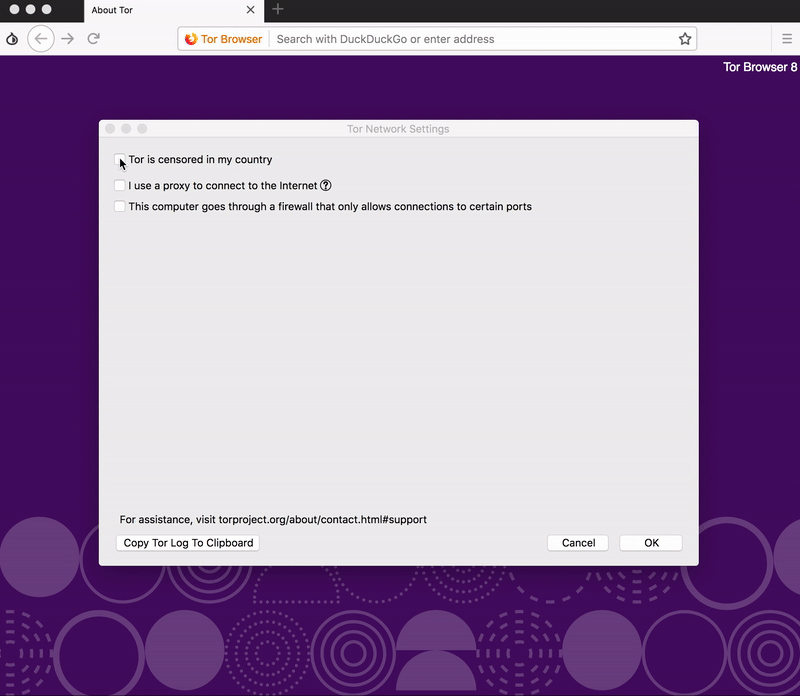
While this sounds good, there are many complications. You must configure Internet applications individually before they'll be able to use Tor, for instance. And the program disables plugins like Flash or Adobe's PDF reader to ensure they can't give away your IP address, so many websites will no longer work. (Though you can selectively restore these plugins if you don't mind potentially leaking identifiable information.)
If you'd like to be more anonymous online, then, Tor can help, but to get the best protection you'll need a clear idea of how the program works. Check the warning section on the Tor website for more information.
Note this is the Alpha Preview of the forthcoming Tor 10.0.
Verdict:
Tor packs a great deal of privacy power, but beware: staying anonymous requires many browsing compromises, and there's plenty of work involved before the program will deliver its best results



Your Comments & Opinion
Protect your computer and enjoy unrestricted internet access when using wifi hotspots
Preserve your anonymity online with this interesting privacy tool
Preserve your anonymity online with this interesting privacy tool
Preserve your anonymity online with this interesting privacy tool
Preserve your anonymity online with this interesting privacy tool
Preserve your anonymity online with this interesting privacy tool
Malwarebytes' next-generation do-everything product
A small but powerful browser toolbar remover
Protect your personal privacy with this exceptionally thorough security tool
Keep your inbox free of spam
Protect your privacy by clearing program and Windows' logs