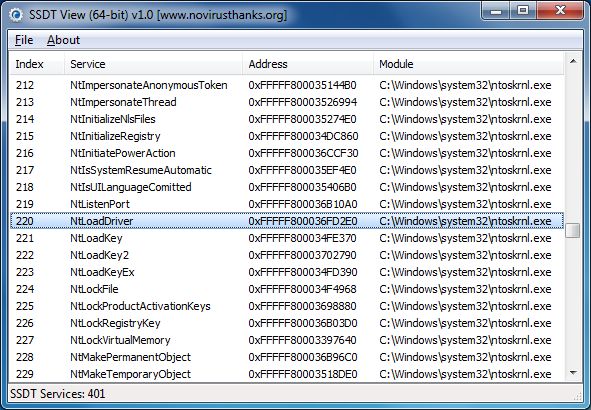
SSDT View is a simple 64-bit (only) tool which does precisely what its name suggested, displaying the key contents of the System Service Descriptor Table (SSDT): you get a list of services, their indexes, addresses in memory, and the module which is supporting them.
Why should you care? Whenever a program carries out some core function in Windows - checks the Registry, reads a file, launches or closes a process and more - Windows will usually pass the command to the relevant function in the SSDT: NtReadFile, say, or NtWriteFile. And so if malware can tweak the table, change one of these memory addresses to point to its own module instead, then it'll be able to take very low-level control of your system, perhaps hiding itself from antivirus software or protecting its processes from termination.
If you suspect your system is infected by malware, then, checking the SSDT for hooks can be a useful step. Anti-rootkit tools can do this for you, but they can be complex and intimidating: SSDT View is much safer and more straightforward, particularly if you're a novice in this field.
Just launch the program, and scroll down the list, checking the Module column. On our test 64-bit Windows 7 PC, this always pointed to the kernel (\Windows\system32\ntoskrnl.exe), which is entirely normal. If you see something else for a few services then that means they've been hooked by the named module, which could be a sign of trouble, although you shouldn't jump to conclusions: the program may be manipulating the SSDT for some legitimate reason. Search for the module name at Google, if you don't recognise it, to try and find out more.
Verdict:
SSDT View is an extremely simple tool which may help you to detect the presence of some otherwise very stealthy malware. If you don't mind the complexity, though, you'll be much better off with a full-strength antirootkit application.








Your Comments & Opinion
Detect and remove rootkits with a click
Detect and remove common rootkits in seconds
Scan a PC for rootkits and other suspect processes
Detect and display some API hooks with this low-level security tool
Detect even the stealthiest of malware with this powerful antirootkit tool
Preserve your anonymity online with this interesting privacy tool
Preserve your anonymity online with this interesting privacy tool
Preserve your anonymity online with this interesting privacy tool
Track and recover your lost or stolen laptop with this free tool
Malwarebytes' next-generation do-everything product