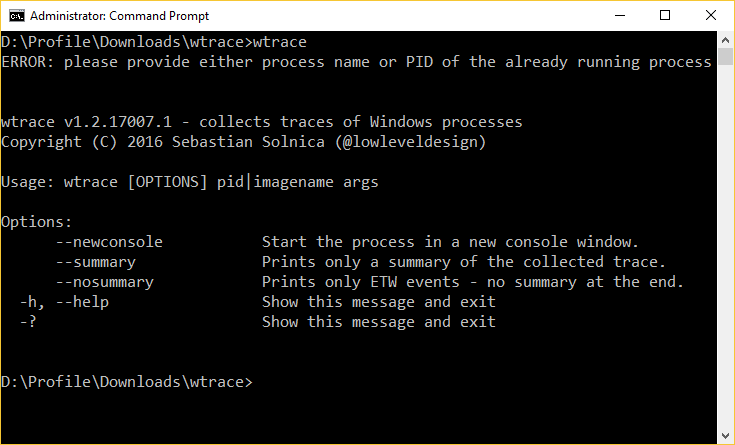
Wtrace is an open-source command line monitor which displays the file I/O, TCP/IP, ALPC and RPC actions (local and remote procedure calls) for a specific process.
Usage is simple, in theory at least. At a minimum, you can run the program from an elevated command line with the name of the process image - wtrace outlook.exe - and it displays file creates, reads, writes, closes, thread starts, procedure calls and more. Monitoring stops when the process closes or you press Ctrl+C.
One issue we noticed immediately is wtrace refused to monitor most processes when specified by name, giving the utterly useless non-specific error code 0x80004005. If you see the same, the workaround is to use the process ID instead (grab it from the PID column in Task Manager and enter something like wtrace 8012).
Once we'd got the program working, it ran without any issues. Actions were displayed in real time at the command line, like this.
1134,4316 (1072) FileIO/Create 'C:\' (0xFFFFFA801D789CA0) rw-
1135,2725 (1072) FileIO/Create 'C:\Windows\Prefetch\MSPAINT.EXE-B4A5B5E8.pf' (0xFFFFFA8023E185A0) ---
1135,5118 (1072) FileIO/Create 'C:\Windows' (0xFFFFFA8023E185A0) rw-
1135,5514 (1072) FileIO/Create 'C:\Windows\SYSTEM32\wow64.dll' (0xFFFFFA801D789CA0) rw-
1135,8384 (1072) FileIO/Close 'C:\' (0xFFFFFA801D789CA0)
When we closed the process, wtrace displayed summaries of various actions. For example, a === TCP/IP === section listed all detected connections with the source and destination IPs, and the total bytes sent and received.
You can take the program further with standard redirect and other tricks. Use - wtrace 14200 > log.txt - to save the output to disk, or use it with Findstr to filter it for specific text.
Verdict:
Process Monitor will be a better monitoring choice for most users, as it records more actions, has built-in filtering and a GUI for ease of use. But if you need a command line tool, RPC and ALPC reports or summaries for TCP/IP and other actions, wtrace could be handy too. Give it a try.




Your Comments & Opinion
Find out exactly what the programs running on your PC are doing
View & manipulate Windows processes
Identify and kill running processes
Monitor file activity, Registry changes, more
Find out more about the Windows services and drivers on your PC
Convert almost any documents to PDF format in a click
Take control over the drive letters assigned to your USB devices
Take control over the drive letters assigned to your USB devices
Get TeamViewer’s best remote control and assist features for free.
Get TeamViewer’s best remote control and assist features for free.