SmartSniff is a tiny packet sniffer which tries to capture and display the TCP/IP packets that pass through your chosen network adapter.
The program can work with Microsoft Network Monitor Driver and WinPcap, but can also work with raw sockets if you've nothing else installed.
To get started, open the program, click the green "Play" button on the toolbar and select the network adapter to use.
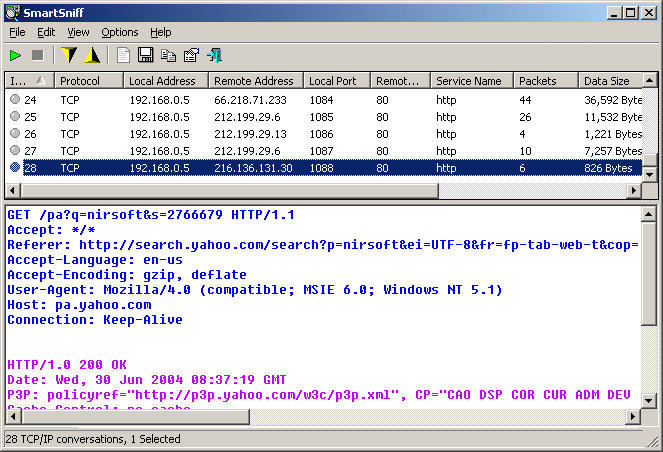
Any background network packets will be captured and various details displayed: protocol, local and remote addresses/ ports/ hosts, service name, data size, capture time, local and remote MAC address, local and remote IP country, and more.
Send an email, open a browser, visit a website or two and more traffic details should appear.
Once you've finished, click "Stop" to stop capture.
Browse down the list to look for interesting packets, perhaps based on the remote host name. Click on any item and the lower pane shows you its contents in either text or hex form.
If this was a POP3 packet, for instance, you might see user names and passwords travelling over the network in plain text.
Browsing down the list, we noticed an odd host name we didn't recognise, clicked the packet and found text showing it related to our antivirus package.
There are a huge number of display and capture options, including the ability to filter traffic by protocol and port.
You can also export the table as an HTML report, or save the captured packets for analysis somewhere else.
Version 2.29:
- Fixed bug from version 2.28: SmartSniff crashed when selecting loopback interface or other network interfaces without connection information.
Verdict:
An excellent packet sniffer, compact, portable and highly configurable.




Your Comments & Opinion
Monitor your network and internet traffic in real time
Monitor your network and internet traffic in real time
Recover lost passwords from network traffic
An updated WinPcap for modern PCs
Capture and monitor network traffic
A comprehensive network monitor/ analyzer
Final release version of Microsoft's Chromium-powered Edge browser
Final release version of Microsoft's Chromium-powered Edge browser
An alternative spin on the Thunderbird email client
An alternative spin on the Thunderbird email client
An alternative spin on the Thunderbird email client